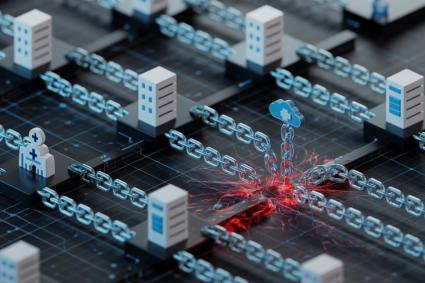
Why Healthcare Vendors Are the Weakest Link in Data Security
Healthcare vendors often handle sensitive patient information but lack strong cybersecurity measures. Weak vendor systems, outdated practices, and poor compliance make them prime targets for hackers, demanding tighter oversight and...